Frequently asked questions
about TACACS+
What is TACACS+?
Terminal Access Controller Access-Control System, aka TACACS+, is an AAA network protocol, which means it is used for access control, authorization, and accounting for network devices such as routers and switches.
- Authentication: TACACS+ allows network devices to communicate with a central server to authenticate users. When a user attempts to log in to a device, the device sends the login credentials to a TACACS+ server to verify the user’s identity. Only after successful authentication does the user gain access.
- Authorization: After authentication, TACACS+ can also provide authorization, which determines what an authenticated user is allowed to do. For example, it can limit a user’s access to resources on a network device, or control which commands they are allowed to run.
- Accounting: TACACS+ keeps track of what authenticated users have done on the network. It logs information such as what commands were entered, providing an audit trail that can be reviewed later. This is useful for troubleshooting and for meeting compliance requirements.
Why do you need TACACS+?
TACACS+ (Terminal Access Controller Access-Control System Plus) is a security protocol used to provide centralized validation of users attempting to gain access to network devices such as routers, switches, and firewalls. Here are several reasons why TACACS+ is used:
- Centralized Authentication: TACACS+ allows network administrators to centrally manage the authentication of users who are accessing network equipment. This simplifies the management of user credentials and permissions.
- Authorization: Beyond authenticating users, TACACS+ also handles authorization, determining what commands or resources a user can access once they are logged into a system. This granularity helps in implementing least-privilege security practices.
- Accounting: TACACS+ can keep a detailed log of what actions users have performed on network devices. This is useful for auditing and compliance purposes, allowing organizations to track who did what, when, and where.
- Granular Control: With TACACS+, administrators can control each aspect of the user interface individually, such as command authorization and command logging, providing more refined access control.
- Security Features: TACACS+ encrypts the entire authentication process, not just the password, safeguarding against eavesdropping and replay attacks. This is an improvement over older systems like RADIUS, which only encrypts the password.
- Separation of Duties: TACACS+ facilitates the separation of duties by providing distinct and separate control over authentication, authorization, and accounting functions. This can be important in larger organizations with complex security policies.
- Scalability: As an organization grows, managing security on individual devices becomes increasingly cumbersome. TACACS+ allows for scalable security management that can grow with the organization’s needs.
How does TACACS+ work?
TACACS+ works based on a client-server model, where the network devices act as clients that communicate with a TACACS+ server. The interaction typically follows these steps when a user attempts to access a network device or service:
- User Login Attempt: When a user attempts to log into a network device (like a router or switch), the device prompts the user for credentials (username and password).
- Credential Verification Request: The network device, acting as a TACACS+ client, packages the user’s credentials into a request and sends it to the TACACS+ server over TCP. The communication between the TACACS+ client and server is encrypted, ensuring that sensitive information is protected during transit.
- Server Authentication: The TACACS+ server receives the request and checks the credentials against its database. If the credentials are valid, the server sends an authentication response back to the device, allowing the user to proceed. If the credentials are invalid, the server denies access, and the user may receive an error message or a prompt to try again.
- Authorization (Optional): If authentication is successful, the device can request authorization for the authenticated user. This step involves the TACACS+ server determining what the user is allowed to do on the device. For example, the server might restrict the user to certain commands or functionalities based on the user’s role or group membership. The server sends an authorization response back to the device, specifying the level of access granted to the user.
- Accounting (Optional): The TACACS+ server can also perform accounting, which records the actions that the user takes while logged in. The device sends accounting start and stop messages to the server, detailing the user’s activities, such as commands entered or configuration changes made. This information can be logged for auditing and compliance purposes.
Is my network vulnerable without TACACS+?
Whether your network is vulnerable without TACACS+ depends on several factors, including your current security measures, network size, and the nature of your operations. TACACS+ primarily provides robust authentication, authorization, and accounting functionalities for device access management. Here are some aspects to consider when evaluating your network’s vulnerability without TACACS+:
- Authentication Practices: Without TACACS+, if your network devices rely on local databases for authentication or use weaker authentication methods, they might be more susceptible to unauthorized access. Centralized authentication, like that provided by TACACS+, helps ensure consistent security policies across all devices.
- Access Control and Authorization: TACACS+ provides granular access control, allowing administrators to specify exactly who can access what resources and what they can do with those resources. Without such controls, your network might allow more privileges than necessary to users, potentially increasing the risk of accidental or malicious changes.
- Audit and Accountability: TACACS+ logs all access attempts and changes made to the network configurations. Without these detailed logs, it may be difficult to track who did what and when, which is crucial for troubleshooting and auditing, particularly in security breach investigations.
- Policy Enforcement: TACACS+ ensures that security policies are consistently enforced across the network. Without it, maintaining uniform policy enforcement can be challenging, especially in large or complex network environments.
- Security of Authentication Data: TACACS+ encrypts the entire authentication process, providing protection against various types of cyber threats, including data interception and replay attacks. Relying solely on less secure methods might expose sensitive data to potential compromise.
- Network Scale and Complexity: In larger or more complex networks, managing access without a centralized system like TACACS+ can be cumbersome and error-prone, potentially leading to security gaps.
- Compliance Requirements: For organizations under regulatory mandates to secure access to network devices and log access events, not having a system like TACACS+ might not only increase security risks but also lead to compliance issues.
What's the advantage of Portnox's cloud-native TACACS+?
Portnox’s cloud-native TACACS+ solution provides several advantages over traditional TACACS+ deployments. These advantages are primarily centered around the benefits of cloud computing, offering enhanced flexibility, scalability, and ease of management. Here are some of the key advantages:
- Cloud-Based Management: By leveraging cloud infrastructure, Portnox’s TACACS+ allows for centralized management of access control policies across multiple locations and devices from a single cloud-based platform. This makes it easier to administer and update policies across a distributed network.
- Scalability: Cloud-native solutions inherently offer scalability, which means organizations can easily adjust their usage based on current needs without having to worry about physical server capacities. This is particularly beneficial for growing businesses or those with fluctuating demand.
- Reduced IT Overhead: Deploying TACACS+ in the cloud reduces the need for organizations to maintain their own physical servers and other infrastructure for their access control systems. This can significantly lower capital expenditures and operational costs related to hardware maintenance and upgrades.
- Enhanced Security: Portnox’s solution can benefit from the robust security measures provided by cloud platforms, including regular updates and patches to defend against the latest security vulnerabilities. Cloud providers typically offer high standards of security that might be hard for individual organizations to achieve on their own.
- High Availability and Reliability: Cloud platforms generally offer high availability configurations and data redundancy to ensure service continuity and minimize downtime. This is critical for access control systems where ensuring constant operational capability is necessary.
- Quick Deployment and Updates: Cloud-native applications can be deployed much faster than traditional on-premises solutions. Updates and new features can also be rolled out more quickly and seamlessly, often without the need for significant downtime or manual intervention.
- Remote Access and Management: With a cloud-based TACACS+ solution, administrators can manage access control policies remotely, which is an advantage for organizations with remote or distributed teams.
- Integration Capabilities: Being cloud-native, Portnox’s TACACS+ may offer better integration capabilities with other cloud-based services and APIs, allowing for a more cohesive security and network management environment.
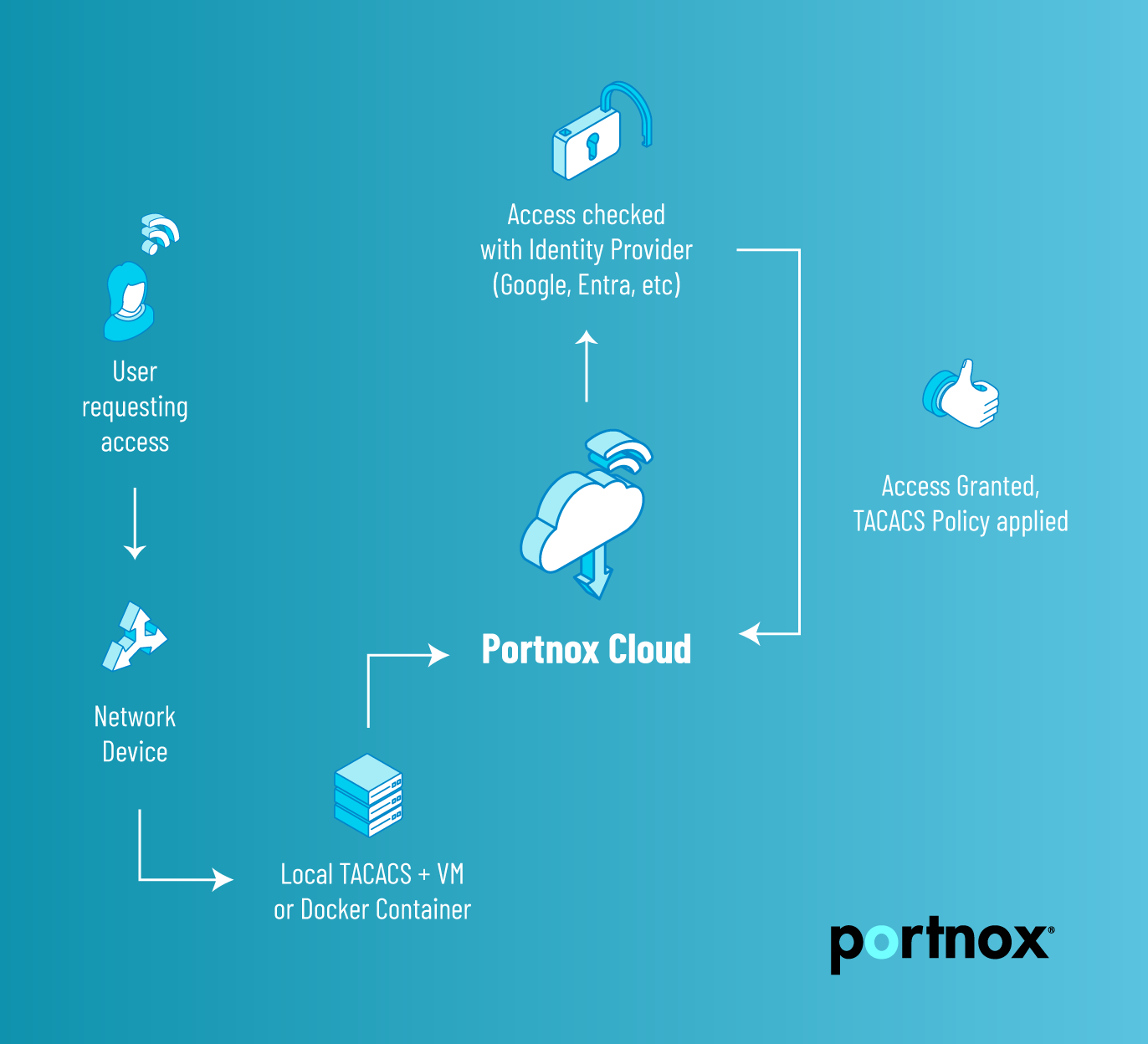
How does Portnox’s cloud-native TACACS+ work?
The Portnox Cloud TACACS+ service is a local server. To set it up, you have two options:
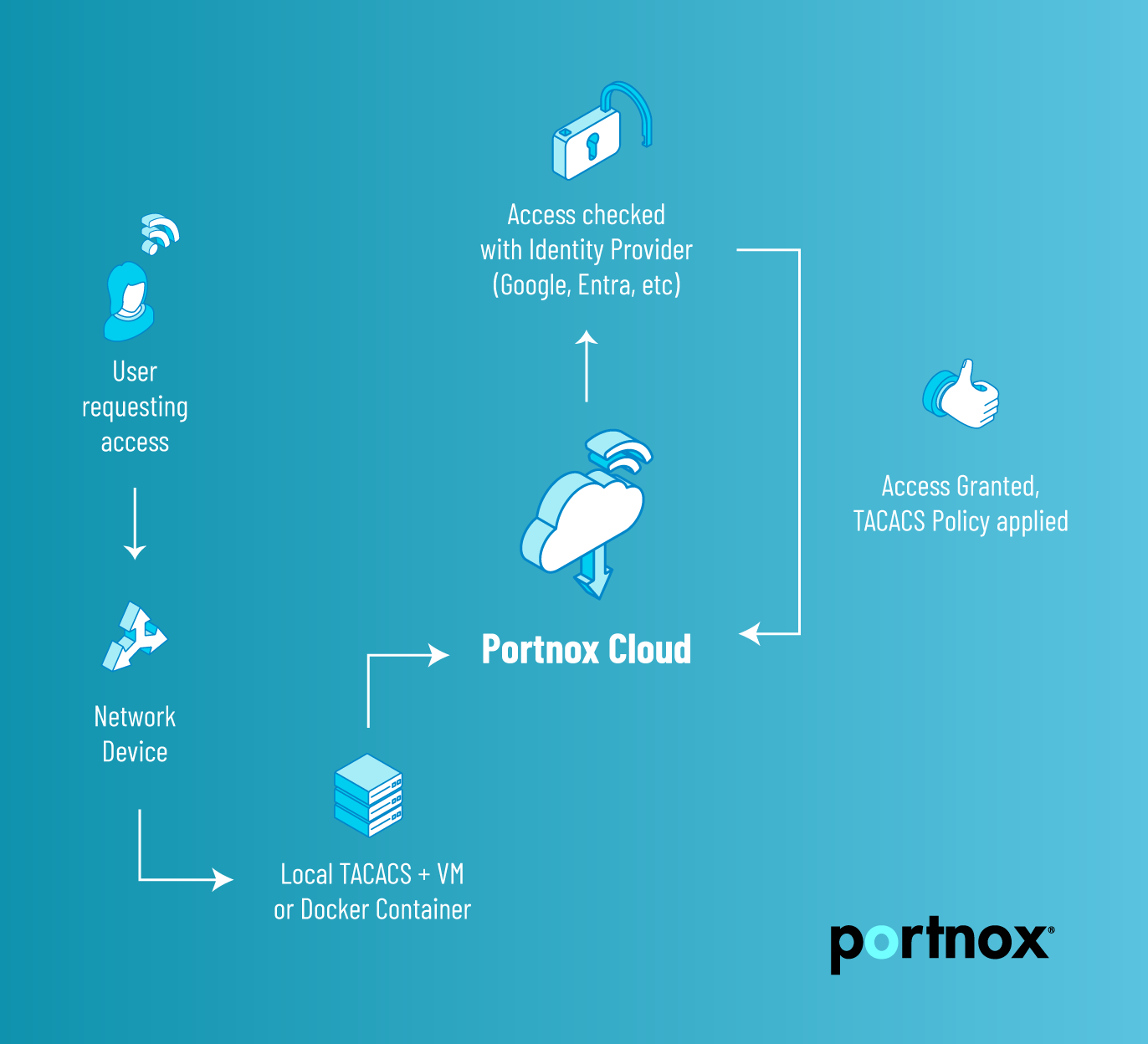
- Virtual Machines: You need to download a virtual machine image and its configuration, deploy it locally, and connect it to your on-premises network.
- Containers: You need to deploy a Docker container locally or in the cloud, and connect it to the on-premises network.
- The local TACACS+ server first checks user authentication by connecting to the cloud RADIUS servers.
- If the user is authenticated, the local TACACS+ server accesses the TACACS+ policy defined in Portnox Cloud, assigned to the user’s group.
- The TACACS+ policy defines user authorization for services, commands, and command attributes on the NAS device. The NAS device is configured for session-based or command-based authorization. If it is configured for session-based authorization, it only requests the session to be authorized. If it is configured for command-based authorization, each command run on the NAS device needs authorization from the TACACS+ server.
- The NAS device then reports user activity details to the TACACS+ server, and the TACACS+ server sends it to Portnox Cloud for accounting purposes. Portnox Cloud administrators can access alerts and troubleshooting logs to see user actions on the NAS devices.
If it's cloud-based, why do I need to download & install anything?
TACACS+ as a protocol has some limitations when it comes to NAT (Network Address Translation) – since NAT strips the originating IP address out of the headers, you lose the ability to enforce specific commands, along with visibility into what was accessed, and what devices the commands were executed against (in other words, the key parts of the Authorization and Accounting of the AAA protocol.) By deploying a local VM or Docker Container on-prem, or in Azure, AWS, etc using ExpressRoute or the equivalent, the NAT limitation is addressed and you can take full advantage of all that TACACS+ has to offer.
What is the difference between RADIUS and TACACS+?
The age-old question: Which AAA protocol is best? RADIUS (Remote Authentication Dial-In User Service) and TACACS+ are both network protocols used for the authentication, authorization, and accounting (AAA) of users who are accessing networked devices and services. Despite serving similar functions, there are key differences in their operation, capabilities, and use cases:
- Protocol Basis and Transport
- RADIUS: Operates over UDP (User Datagram Protocol), making it less reliable in terms of delivery assurance than TCP-based protocols. However, UDP’s simplicity can be an advantage in less complex scenarios.
- TACACS+: Uses TCP (Transmission Control Protocol) for its communications, ensuring reliable delivery of packets. TCP’s connection-oriented nature is beneficial for the encryption and integrity of data exchanged between the AAA server and client.
- Encryption and Security
- RADIUS: Encrypts only the password in the access-request packet, leaving other information such as usernames and the rest of the packet data unencrypted. This can be a security concern in environments requiring high security.
- TACACS+: Encrypts the entire body of the protocol packet, providing more comprehensive security for AAA data.
- AAA Function Segregation
- RADIUS: Combines authentication and authorization into a single step, which can simplify configuration but offers less flexibility than TACACS+. Accounting is handled separately.
- TACACS+: Separates authentication, authorization, and accounting processes. This separation allows for more granular control over access and permissions, making TACACS+ more flexible in complex network environments.
- Interoperability and Use Cases
- RADIUS: More commonly used for network access scenarios, such as VPN access, wireless authentication, and dial-up connections. Its simplicity and support by a wide range of hardware and software make it a popular choice for controlling network access.
- TACACS+: Often preferred for administrative access to network devices like routers, switches, and firewalls due to its detailed command authorization and accounting capabilities. It is highly favored in environments that require detailed auditing and control over individual user activities.
